Industrial IoT (IIOT) Reference Architecture
By Kuldeep Singh
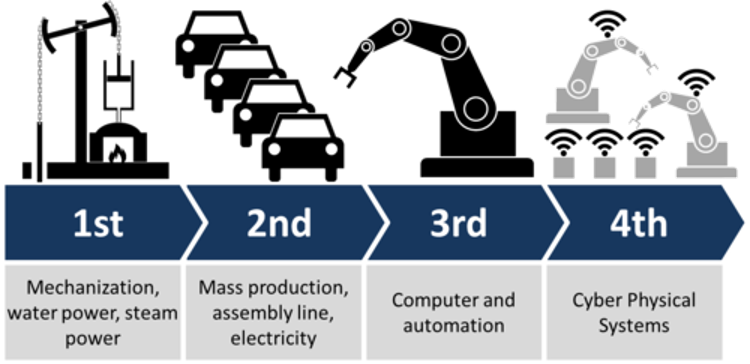
- 5 minutes read - 886 wordsThe industry has been going through an evolution. Industry 4.0 is the fourth industrial revolution where the key will be on digital transformation.
Industry 4.0 creates what has been called a “smart factory”. Within the modular structured smart factories, cyber-physical systems monitor physical processes, create a virtual copy of the physical world and make decentralized decisions. Over the Internet of Things, cyber-physical systems communicate and cooperate with each other and with humans in real time, and via the Internet of Services, both internal and cross-organizational services are offered and used by participants of the value chain.
The core of industry 4.0 is technology. Digital trust and data analytics are the foundation of this. Focus will be on people and culture to drive transformation. All this is achieved through Industrial Internet of Things (IIoT) which falls under the ecosystem of IoT. But the industry is in complex of itself, where there is a need to connect different kind of heterogeneous systems, high availability and scalability without compromising on the security aspect of the system. Hence there a need to have a specific architecture reference specially designed for the IIoT. This document is all about the architecture reference for IIoT.
Foundation Principle and Concept
Agility
With the ever-growing challenges and opportunities that face companies today, a company’s IT division is a competitive differentiator that supports business performance, product development, and operations. A leading benefit companies seek when creating an IIoT solution is the ability to efficiently quantify opportunities. These opportunities are derived from reliable sensor data, remote diagnostics, and remote command and control between users and devices. Companies that can effectively collect these metrics open the door to explore different business hypotheses based on their IIoT data. For example, manufacturers can build predictive analytics solutions to measure, test, and tune the ideal maintenance cycle for their products over time. The IIoT lifecycle is comprised of multiple stages that are required to procure, manufacture, onboard, test, deploy, and manage large fleets of physical devices.
Interoperability
The ability of machines, devices, sensors, and people to connect and communicate with each other via the Internet of Things (IoT) or the Internet of People (IoP). In order for a company’s IoT strategy to be a competitive advantage, the IT organization relies on having a broad set of tools that promote interoperability throughout the IoT solution and among a heterogeneous mix of devices.
Information transparency
The ability of information systems to create a virtual copy of the physical world by enriching digital plant models with sensor data. This requires the aggregation of raw sensor data to higher-value context information.
Security
Security is an essential quality of an IIoT system and it is tightly related to specific security features which are often a basic prerequisite for enabling Trust and Privacy qualities in a system. Ability of the system to enforce the intended confidentiality, integrity and service access policies and to detect and recover from failure in these security mechanisms.
Performance and Scalability
This perspective addresses two quality properties that are closely related: Performance and Scalability. Both are, compared to traditional information systems, even harder to cope with in a highly distributed scenario as we have it in IIoT. The ability of the system to predictably execute within its mandated performance profile and to handle increased processing volumes in the future if required. Any system with complex, unclear, or ambitious performance requirements; systems whose architecture includes elements whose performance is unknown; and systems where future expansion is likely to be significant.
Architecture Components
Below is the high level architecture of a IIoT System.
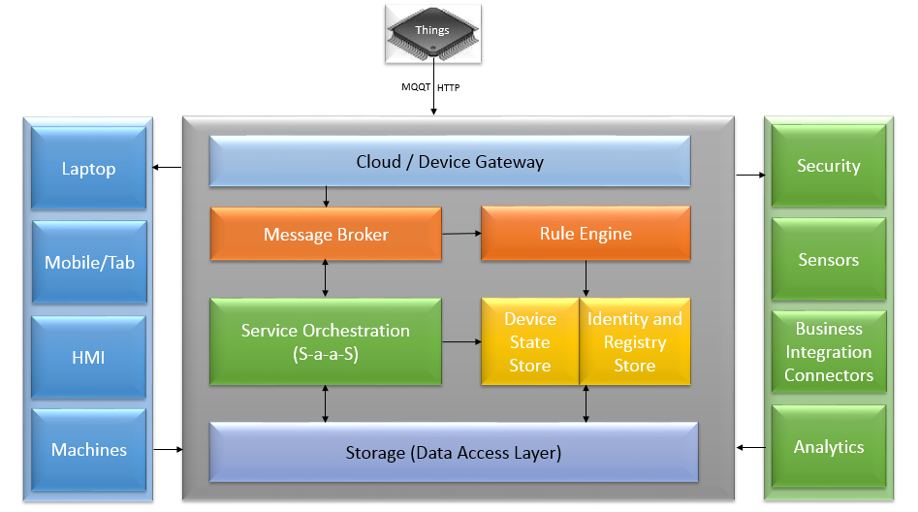
Protocols (Device Connectivity)
One of the issues encountered in the transition to the IIoT is the fact that different edge-of-network devices have historically used different protocols for sending and receiving data. While there are a number of different communication protocols currently in use, such as OPC-UA, the Message Queueing Telemetry Transport (MQTT) transfer protocol is quickly emerging as the standard for IIoT, due to its lightweight overhead, publish/subscribe model, and bidirectional capabilities.
Service Orchestration
Service orchestration would happen at this level, where the system will interact with different business adaptors. The services are more of the nature of event based and it is based out the principle of Reactive Manifesto. The services will be responsive, resilient, elastic and message driven.
Rule Engine
The Rules Engine makes it possible to build IIoT applications that gather, process, analyze and act on data generated by connected devices at global scale without having to manage any infrastructure. The Rules Engine evaluates inbound messages published into IIoT and transforms and delivers them to another device or a cloud service, based on business rules you define. A rule can apply to data from one or many devices, and it can take one or many actions in parallel.
Device Provisioning (Data Identity and State Store)
Device provisioning uses the identity store to create identities for new devices in the scope of the system or to remove devices from the system. Devices can also be enabled or disabled. When they are disabled, they have no access to the system, but all access rules, keys, and metadata stay in place.
Security
Security is going to be one the fundamental to the system. The data across every tier would go through proper security mechanism.
This article was also supported by Ram Chauhan
#architecture #IOT #industrial #Cloud #smart factory #Industry 4.0 #enterprise #technology